VTB Bank Breached by GURMO Cyber Operators
Detailed plans about its FSB Headquarters branch are released
GURMO hackers breached the network security of VTB bank and downloaded financial records, videoconference calls, schematic diagrams of the bank’s industrial control systems that control electricity, water, heat, and drainage.
Background
VTB bank is Russia’s second largest bank. In 2011, the bank was a major source of funding for Yuri Milner’s and Alisher Usmanov’s investments in Facebook and Twitter via DST Global. In 2014, the U.S. Treasury OFAC added the bank to its Sanctions list, followed by the EU, Canada, and other countries due to Russia’s annexation of Crimea and invasion of Ukraine. New sanctions were issued in 2022 by the U.S. and the U.K. in response to Russia’s war against Ukraine.
Approximately 97% of the bank’s shares are owned by three agencies of the Russian government:
12.13% of (capital) shares – Federal Agency for State Property Management (Russia)
32.88% of (capital) shares – Ministry of Finance (Russia)
47.22% of (capital) shares – Deposit Insurance Agency of Russia
FSB Branch
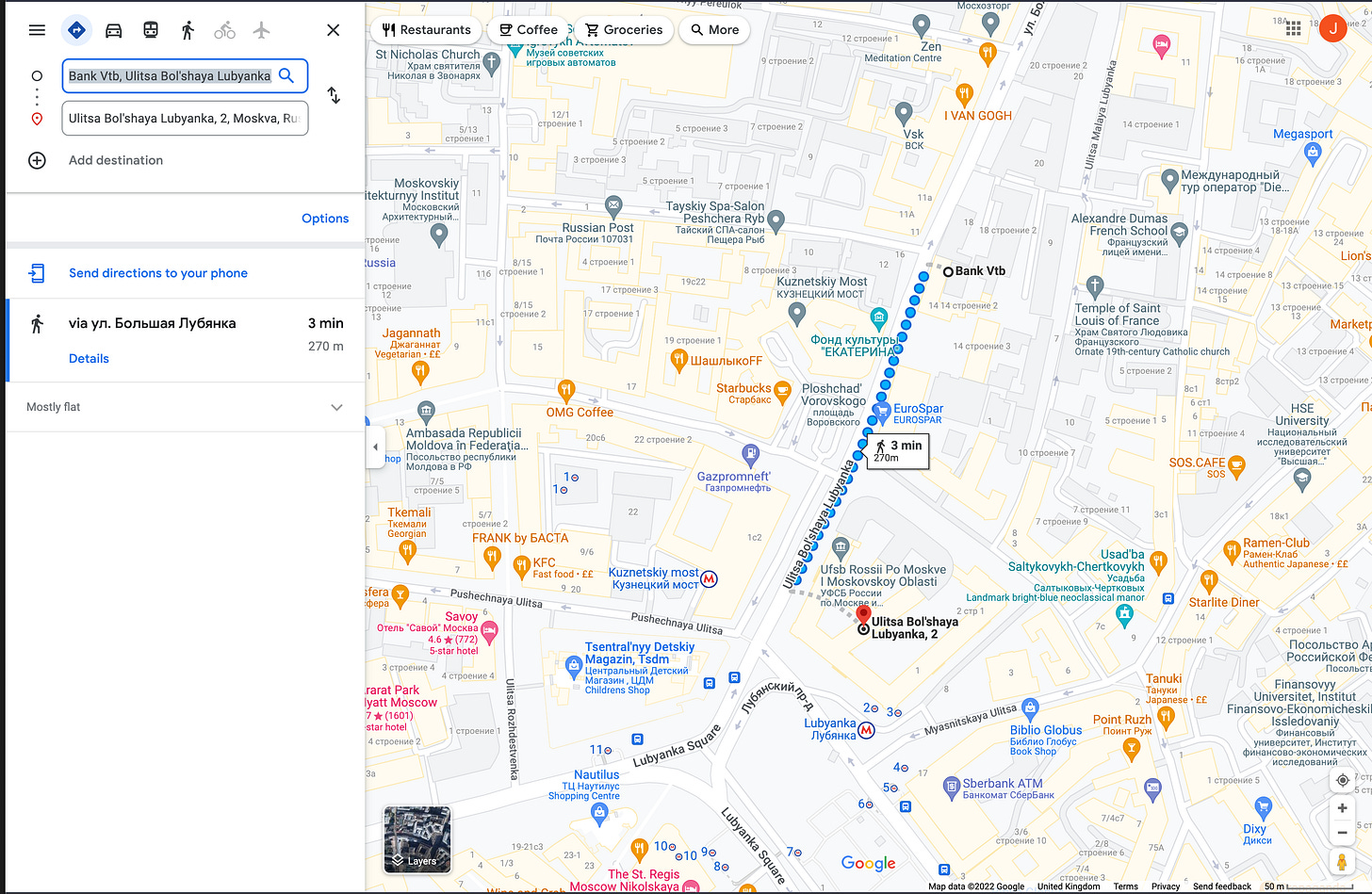
Some of the files captured by GURMO are for construction of an office for private clients on Lubyanka street, about a three minute walk from FSB headquarters.
Ukraine’s government will be using the information obtained in this breach to find and seize Russian oligarchs’ funds along with a parallel effort being waged by the U.S. Treasury and Justice Departments Multi-lateral Russian Oligarch Task Force.
A small portion of the files that have been shared with Inside Cyber Warfare are available for download for paid subscribers. The rest are undergoing analysis by the government of Ukraine and will be shared with its U.S. and U.K. allies.
Contents include:
The Pre-Project Survey Report for VTB Bank’s additional office at Lubyanka
Photos of the project site
Design of the bank’s SCADA system
Design of the bank’s energy system