Rostelecom's Information and Communications Design Company "PJSC Giprosvyaz" Was Breached
This could lead to foreign intercepts of Putin's Summit meetings with world leaders
The above is a promotional video for OJSC Giprosvyaz in Belarus
In order to understand the importance of this breach of PJSC Giprosvyaz, announced for the first time today but conducted several years ago by hackers working for Ukraine’s Main Directorate of Intelligence of the Ministry of Defense (GUR), you have to know something about Giprosvyaz’s history.
Origin
In 1932, Giprosvyaz began as a Trust named “Svyzaproekt” under the People’s Commissariat of Communications of the USSR with two branches: Leningrad and Kyiv.
In 1951, the Svyzaproekt Trust became the State Institute for Research and Design of Communication Facilities - “Giprosvyaz”.
In 1997, the Giprosvyaz Institute became an open joint stock company, OJSC Giprosvyaz, held by OJSC Svyazinvest, where it became the leading design organization for the telecommunications companies of the Svyazinvest Group.
Over the next twenty years, Svyazinvest Group became PJSC Rostelecom and OJSC Giprosvyaz became PJSC Giprosvyaz, a Rostelecom subsidiary, which it remains today.
Work
It sets technical policy and developer guidelines that must be followed by all communications designers, regardless of department affiliation.
Russia’s Ministry of Communications relies on Giprosvyaz to develop industry regulations and GOSTs. For example:
“Unified General Scheme for the Development of Telecommunication Networks of Interregional Communication Companies and OJSC Rostelecom”
“The General Scheme for the Development of the International Public Fax Service Burofax of the Russian Federation until 2015"
"General scheme for the creation and phased development of the federal public mobile radiotelephone network in Russia in the 450 MHz band and the IMT-450-MC standard"
In preparation for the 2014 Olympics in Sochi, Giprosvyaz won a competition to design and build a world-class telecommunications and information infrastructure in Sochi to include “creating an infrastructure for digital television and radio broadcasting (cost - 1.1 billion rubles), fiber-optic communication lines (FOCL) with a length of 700 km (923 million rubles), a TETRA trunking communication network for government agencies (900 million rubles) and facilities electric and postal communications in Krasnaya Polyana and two Olympic villages (150 million rubles).”
Sochi
Besides hosting the 2014 Winter Olympics, Sochi is where both President Vladimir Putin and Prime Minister Dmitry Medvedev maintain residences, and both residences would require advanced information and communications networks, almost certainly designed, planned, and installed by Giprosvyaz. Besides Putin’s personal palace shown below, there’s the official summer residence Bocharov Ruchey.
Sochi is also where Putin conducts many of his summits with international leaders such as Belarus President Lukashenko, Turkey’s President Erdogan, and with the Chairman of the African Union Maki Salem who Putin met with as recently as last week due to concerns over the food crisis caused by the Russian blockade of Ukrainian wheat exports.
How To Compromise A Summit Meeting Without Fear of Detection
If you’re a foreign intelligence service that wants to listen in on a Summit meeting between two world leaders, there aren’t any easy options. You would have to defeat a number of countermeasures that have already been put into place to prevent eavesdropping, or find and recruit someone who had access to what had transpired during the meeting.
On the other hand, if you had access to the company that designed and installed the network used by the city where the meeting was held, and information and communications blueprint for the building where the meeting took place, and the exact location for all of the communication outlets broken down by floor and by room, imagine how much easier your job would be.
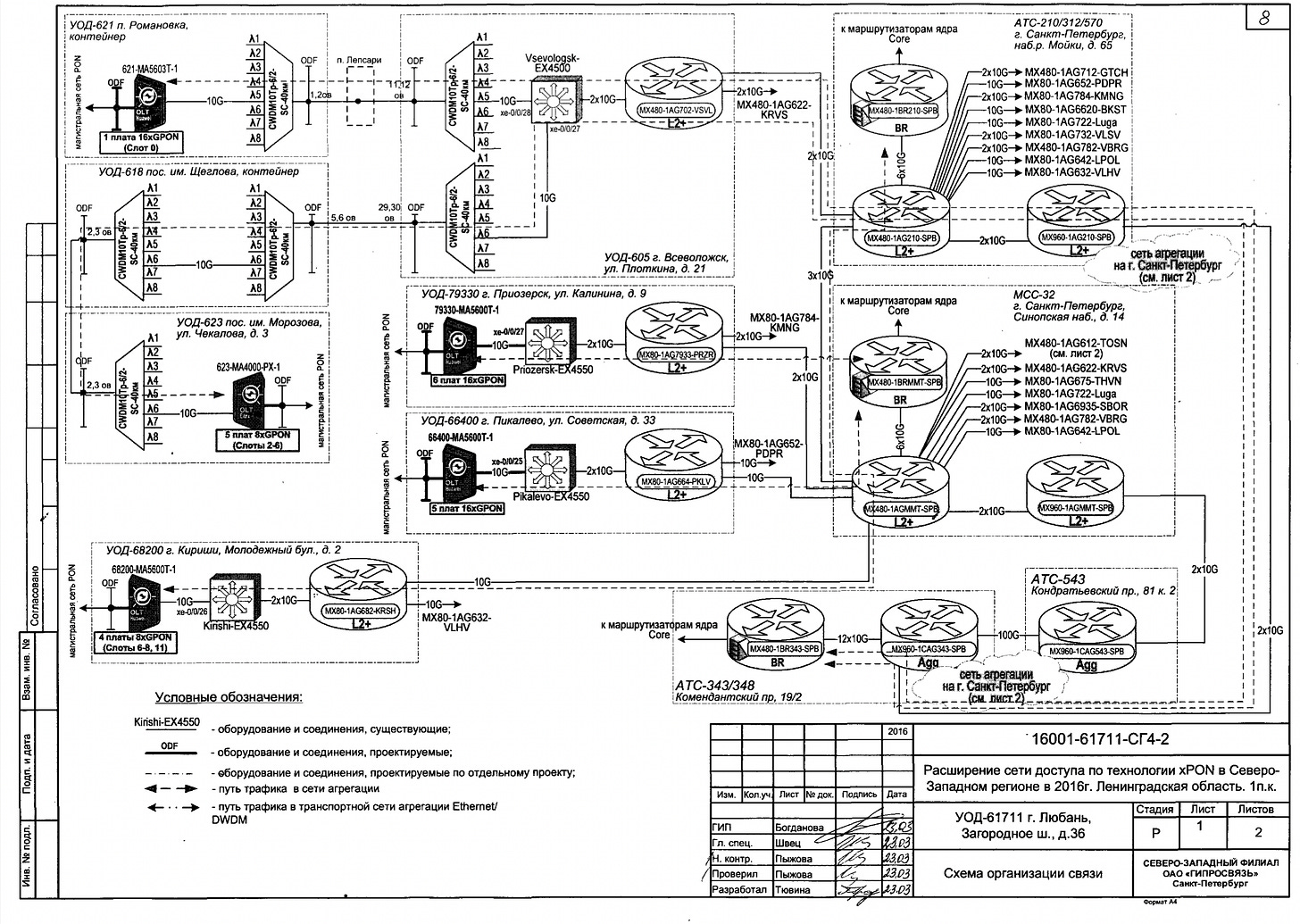
The above images aren’t for Sochi or for an important summit. They are part of a 20 MB cache of internal Giprosvyaz documents, spreadsheets, and diagrams provided to Inside Cyber Warfare by GRU hackers as a sample. GRU maintains complete access to PJSC Giprosvyaz at the time of this writing.
Inside Cyber Warfare subscribers may access the download below the break.